
BLOG
TECHNOLOGY UPDATES & MORE

SnowCap’s Soc II and Hippa Journey
Security and trust aren’t just priorities—they’re foundational to everything we build and deliver. Today, we’re proud to announce a major milestone in that commitment: SnowCap has officially achieved both SOC 2 Compliance and HIPAA Compliance.

Navigating the CMMC Accreditation Odyssey
Embark on a transformative journey in cybersecurity with CMMC accreditation. The odyssey begins by demystifying the intricate CMMC framework, unveiling its secrets for informed decision-making. SnowCap simplifies the journey, offering a quick self-assessment to illuminate strengths and spotlight potential gaps. Choose your strategic epic, collaborating with trusted allies, the CMMC Accredited Bodies (CABs), and let SnowCap guide you through the complexities. This isn't just compliance; it's a proclamation of cybersecurity prowess in the new era.

From our CTO - VMware Ambiguity: Unraveling The Implications
Broadcom's VMware acquisition signifies both evolution and uncertainty. As VMware embraces simplicity and subscription models, questions arise about the impact on existing solutions, the flexibility of subscription models, and the readiness of partners for this shift.
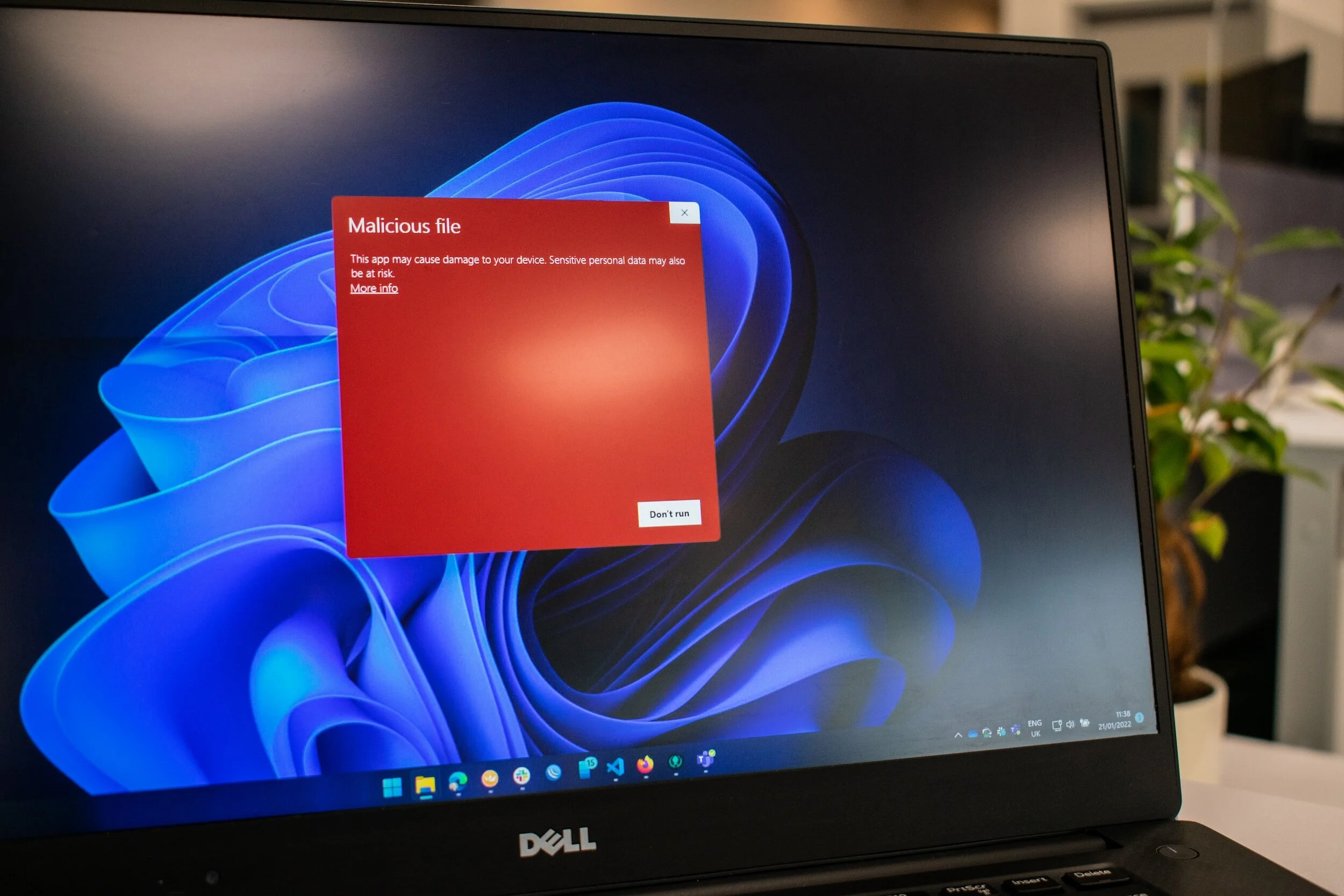
Endpoint Hardening: Fortifying Your Defenses
In the ever-evolving world of cybersecurity, the imperative to fortify digital defenses has never been more crucial. Enter endpoint hardening—a strategic approach that transforms individual devices into cyber heroes. This blog navigates the complexities of endpoint hardening, spotlighting vulnerability remediation, and emphasizing the pivotal role of advanced patch management techniques. As we delve into the critical process of remediation verification through scanning, the urgency of staying ahead of cyber threats becomes apparent. To amplify your defense, discover SnowCap's Patch Guardian service—a comprehensive solution with fully automated tools. It seamlessly integrates into existing tool stacks, offering a layer of protection beyond conventional measures. Trust SnowCap to elevate your cybersecurity posture and navigate the ever-adapting landscape of digital threats. Secure your endpoints, verify your defenses, and usher in a new era of cybersecurity resilience.

Navigating the CMMC Landscape: The Waiting Game Continues...However!
In the ever-surging tides of cybersecurity, mere compliance is no longer sufficient—it's a race to stay ahead, and the finish line is ever-shifting. Enter the Cybersecurity Maturity Model Certification (CMMC), a beacon beckoning organizations into a new era of fortified security. Our journey through this electrifying evolution unfolds in the pages of the eye-opening WashingtonTechnology.com article, "Waiting Game Continues with the Release of Draft CMMC Rule."

Safeguarding DoD Business: Unraveling the Value of CMMC for Subcontractors
Confronting CMMC requirements is an investment in the longevity and competitiveness of a subcontractor's DoD business.
